Incident Response Analyst Resume Example
Market Insights
Software Engineering
Salary Range
Salary Trend
Mar 2025 – Feb 2026
12-Month Trend
Average advertised salaries have increased by 2.4% over the past 12 months based on 117,730 current job postings.
Key Skills
US market data · Source: Adzuna · Updated Mar 2026
How useful was this template?

How useful was this template?
Editorial Notes
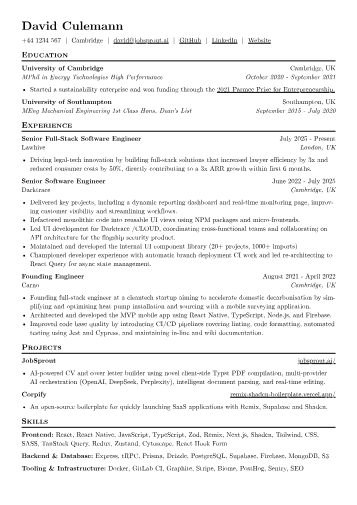
For Incident Response Analysts in Technology, a resume must immediately convey a candidate's ability to mitigate cyber threats under pressure and conduct thorough forensic analysis. Hiring managers specifically seek quantifiable achievements detailing incident containment, eradication, and recovery, alongside expertise in root cause analysis. Mentioning certifications such as GIAC GCIH or GCFA is vital, as is familiarity with SIEM platforms, EDR solutions, SOAR tools, and frameworks like MITRE ATT&CK. Concrete examples of reducing mean time to detect or respond, or successful threat hunting engagements, demonstrate the expected blend of speed and technical depth.
The JobSprout example effectively highlights these critical aspects. Achievements are quantified by detailing the reduction in incident resolution times or the scope of vulnerabilities identified and remediated. Skills are logically grouped, distinguishing between core methodologies like malware analysis or threat intelligence, and specific tools such as Splunk, CrowdStrike, or scripting languages like Python. Key certifications are prominently displayed, providing instant credibility. The template's structure clearly communicates a candidate's proficiency across the entire incident lifecycle, from initial alert to post-mortem reporting.
This template was built with JobSprout and can be remixed to create your own tailored Incident Response Analyst resume. Customize it to reflect your unique experience and specific achievements.
Market Insights
Software Engineering
Salary Range
Salary Trend
Mar 2025 – Feb 2026
12-Month Trend
Average advertised salaries have increased by 2.4% over the past 12 months based on 117,730 current job postings.
Key Skills
US market data · Source: Adzuna · Updated Mar 2026
Frequently Asked Questions
Related Articles
![How to Write a CV for Tech Applications [2026 Guide]](/thumbnails/cv-for-tech-applications.webp)
How to Write a CV for Tech Applications [2026 Guide]
Learn how to write a software engineering CV that gets interviews. Real template analysis, what hiring managers look for, and common mistakes to avoid.
![How to Write a CV That Shows Startup Experience [2026 Guide]](/thumbnails/cv-for-startup-engineers.webp)
How to Write a CV That Shows Startup Experience [2026 Guide]
Learn how to write a CV that showcases founding engineer and startup experience. Real example from JobSprout's creator, what hiring managers look for, and how to position breadth as a strength.